Key Highlights
- There have been many cyber attacks that have taken place in the history of cryptocurrency, that costed billions of dollars loss to investors
- In this attack, hackers have exploited small vulnerabilities and loopholes that could have easily identified with better security measures
The cryptocurrency sector has lost billions of dollars to hacks, exploits, and scams since the launch of Bitcoin in 2009. According to the Chainalysis report, more than $3.4 billion was stolen in 2025 alone, while the worst year was 2022, when losses reached $3.7 billion.
While these cyber attacks seem technically complex, there is a startling pattern among all these cyber attacks. Not all of them were caused by unbreakable code or genius-level hackers finding impossible flaws. They happened because of small mistakes or ignorance, such as a lack of security measures or audits. A single point of failure in the system, or it could be a simple human complacency when everyone assumed someone else was watching.
These simple mistakes cost billions of dollars. These attacks have destroyed companies, ruined the reputation of the crypto companies, and destroyed many people’s lifetime savings. After such hacks, there are so many incidents where people have taken their own lives after watching years of work vanish in minutes.
The good news is that most of these cyber attacks could have been prevented. Not with advanced cryptography or secret techniques known only to elite security teams. But with some simple precautions, new crypto businesses can adopt.
1. Mt. Gox
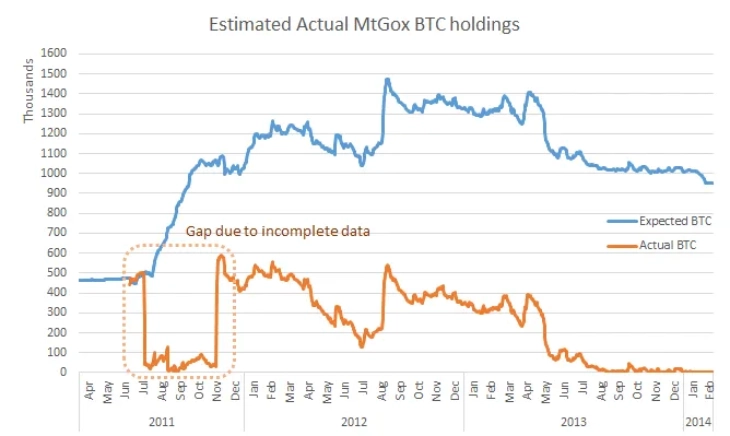
Once, Mt. Gox was used for 70% of the global Bitcoin volume. In February 2014, Mt. Gox collapsed after losing approximately 850,000 Bitcoin. At that time, that was worth about $450 million. Based on today’s price, this stash is around $54 billion.
The exchange initially mentioned “transaction malleability” as a reason behind this cyber attack. This is a known quirk in the Bitcoin protocol, first identified in 2011, where attackers can slightly alter a transaction’s ID without changing its validity.
Mt. Gox’s withdrawal system watched for the original transaction ID. When it did not appear on the network because the ID had been altered, the platform mistakenly resent the coins. This allowed hackers to withdraw the same funds twice.
(Source: trakx.io)
However, there was a different story that came into light after the investigation. Transaction malleability actually accounted for only about 386 Bitcoins of total loss. The bulk of the missing funds came from poor internal controls, excessive exposure in hot wallets, and thefts that went undetected over many years. CEO Mark Karpelès has also admitted that there were systemic loopholes in the exchange.
How Could This Have Been Prevented?
A small coding mistake and the failure to update software became the most infamous exchange collapse in crypto history.
There is a simple lesson one can learn from this Mt. Gox hack. It is important to run updated software and monitor known vulnerabilities through sources like BitcoinTalk or CVE databases. Use multisignature wallets and cold storage for the majority of funds.
Never keep users’ money in hot wallets apart from what is needed for daily withdrawals. If Mt. Gox had implemented proper ID validation and separate storage, the attack would have been stopped early.
2. The DAO Hack
The DAO was a venture fund developed on Ethereum. It raised $150 million worth of ETH from investors, making it one of the largest crowdfunding projects in crypto history at the time.
On June 17, 2016, this project was compromised. A hacker drained 3.6 million ETH from The DAO, worth about $50 million then, which is tens of billions today. The attack used a method called “reentrancy”.
The flaw was in the smart contract’s withdraw function. The code sent ETH to users before updating their balance. The attacker created a malicious contract that called the withdraw function. When the DAO sent ETH to this contract, the contract’s fallback function automatically triggered.
They called withdraw again. Because the balance had not been updated yet, the DAO sent more ETH. This loop repeated over and over. By doing this, the hacker drained funds in seconds.
The code failed to implement a basic security pattern known as “Checks-Effects-Interactions,” or CEI. It also lacked something called a reentrancy guard, which would have prevented this exact scenario.
The attack was so devastating that it split the Ethereum community. Some wanted to reverse the hack by rewriting the blockchain’s history. Others wanted the code to stay as written, no matter the cost. The result was a hard fork that created two separate blockchains. The first one is Ethereum, which reversed the hack. The second one is Ethereum Classic, or ETC, which kept the original chain intact.
How Could This Have Been Prevented?
Developers must follow the CEI pattern every time they write code. It is important to check the condition first, then update the contract’s state, and only then interact with external addresses. They should also use OpenZeppelin’s ReentrancyGuard modifier, which is a simple tool that blocks reentrancy attacks automatically. Most importantly, they must go through third-party audits by experienced security firms.
Conclusion
Apart from these cyber attacks, there are many hacks, scams, and social engineering attacks that have happened in the history of crypto. One can take lessons from these attacks by studying them in detail to fortify today’s crypto world. Minor loopholes or ignorance in security have already ruined the name of the crypto community, and it is crucial to avoid such incidents in order to expand this digital asset sector.
Also Read: On-Chain Derivatives 2026: Find Out Why They Are Outpacing CEXs
See less



