- KelpDAO attacker transferred $176 million worth of stolen funds to new wallets using THORChain, Umbra, Chainflip, and BitTorrent.
- Investigators report ongoing laundering attempts, with funds moved across chains via Thorchain and smaller amounts routed through privacy tools.
- The exploit exposed gaps in DeFi security setups, as reliance on a single validation system allowed forged transactions and a $290 million breach.
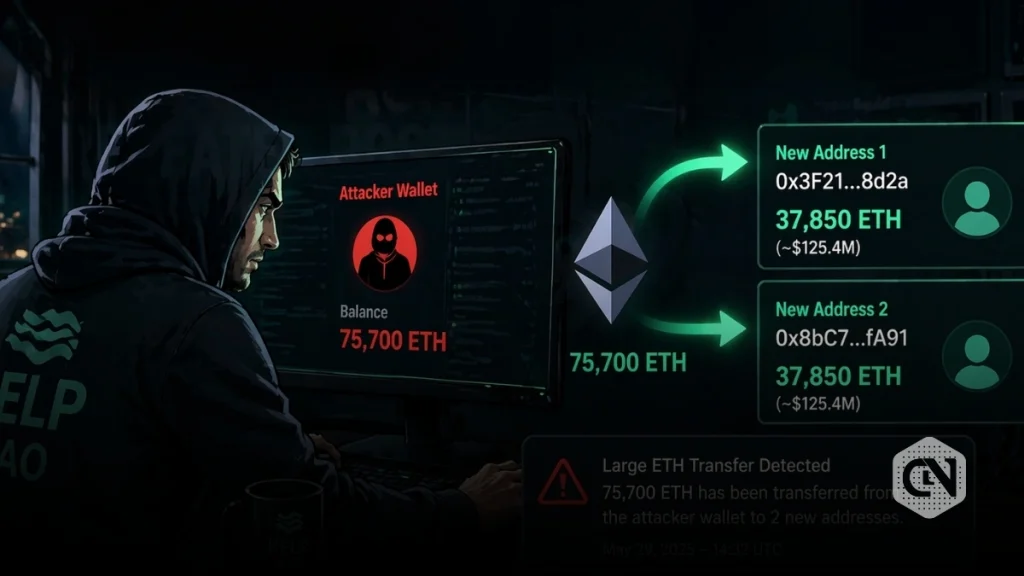
KelpDAO hacker has reportedly started laundering approx $176 million in stolen funds. On-chain data platform, PeckShield revealed that the attacker is currently moving small amounts of money from the Ethereum network to Bitcoin by using services such as THORChain, Umbra, Chainflip, and BitTorrent. This development comes hours after PeckShield data confirmed that 75,700 ETH linked to the exploit was transferred to two new wallet addresses.
KelpDAO Attack: Latest Updates
This transaction comes shortly after a significant intervention by the Arbitrum Security Council. The council successfully froze 30,766 ETH connected to the exploit. The frozen amount is valued at nearly $71 million. Irrespective of this action, the attacker still controls the remaining 75,700 ETH on the Ethereum network, which is worth roughly $175 million at current prices.
The recovery process carried out by the Arbitrum Security Council has drawn attention across the crypto industry. According to an analysis shared by Dragonfly General Partner Haseeb Qureshi, the freeze was executed through a system-level transaction. This type of transaction, known as ArbitrumUnsignedTxType, cannot be initiated by regular wallet users. It can only be deployed through the network’s core system, specifically via ArbOS.
The operation did not involve reversing transactions or rewriting blockchain history. Instead, it functioned as a direct state-level intervention. The attacker’s private key remains active, meaning it can still sign transactions. But, the ETH held in the affected address was moved by the system itself, and placed it out of the attacker’s reach. This action reflects the emergency powers granted to the Security Council under extreme conditions.
The council stated that the move was necessary to protect the ecosystem. It confirmed that the intervention did not impact other users, applications, or chain activity. The recovered funds were transferred into a secure, frozen wallet. Any further movement of these assets will require coordination between custodians and relevant authorities.
At the same time, tracking efforts suggest the attacker has already begun laundering part of the stolen funds. On-chain investigator ZachXBT reported that assets are being moved from Ethereum to Bitcoin using cross-chain protocols such as Thorchain. In addition, a smaller portion, around $78,000, has been routed through privacy tools like Umbra. These methods are commonly used to reduce traceability and complicate recovery.
The exploit itself dates back to April 18, when KelpDAO suffered a major breach. According to an incident report released by LayerZero Labs, the attack resulted in losses of around $290 million. Early findings point to a compromise in the RPC infrastructure linked to the Decentralized Validation Network. The attacker managed to control certain RPC nodes and used a coordinated denial-of-service attack to force the system into relying on malicious nodes.
This allowed the attacker to forge cross-chain messages and execute unauthorized transactions. The issue was traced back to KelpDAO’s use of a single validation setup. The protocol had not executed a multi-layered validation structure, which could have detected or prevented the forged activity. LayerZero confirmed that its core protocol remained unaffected and that other apps using stronger configurations were not impacted.
All compromised infrastructure has since been replaced, and the affected systems are now functional again. LayerZero has urged other projects to opt for multi-validator setups to reduce similar risks. It has also paused certain services tied to weaker configurations and is working with global authorities to trace the stolen funds.
Several reports have linked the attack to North Korea’s Lazarus Group, a well-known state-backed hacking collective. Even as the investigation is ongoing, the scale and method of the exploit align with previous incidents attributed to the group.
The incident has also triggered criticism of security practices within decentralized finance. Ripple’s CTO, David Schwartz recently shared that many protocols have access to strong security tools but often avoid using them due to added complexity costs.